Windows Defence Unit
Posted: March 8, 2014
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 14 |
| First Seen: | March 10, 2014 |
|---|---|
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
 Windows Defence Unit is a fake anti-malware program that doesn't let its crippling deficiencies in actual threat detection slow down Windows Defence Unit from launching fraudulent pop-up warnings and imitation 'system scans'. While malware researchers have acquired a long familiarity with other members of Windows Defence Unit's family, which rotates through their brand names frequently, Windows Defence Unit continues to be a threat to modern PCs through its fraudulent security features, including some functions that may block other programs automatically. The use of actual anti-malware software is encouraged for removing Windows Defence Unit, which should be considered nothing other than a threat to your PC – and to your wallet.
Windows Defence Unit is a fake anti-malware program that doesn't let its crippling deficiencies in actual threat detection slow down Windows Defence Unit from launching fraudulent pop-up warnings and imitation 'system scans'. While malware researchers have acquired a long familiarity with other members of Windows Defence Unit's family, which rotates through their brand names frequently, Windows Defence Unit continues to be a threat to modern PCs through its fraudulent security features, including some functions that may block other programs automatically. The use of actual anti-malware software is encouraged for removing Windows Defence Unit, which should be considered nothing other than a threat to your PC – and to your wallet.
The Software that does Everything Except Defend Your Computer
Windows Defence Unit merely is one of a series of long-running fake anti-malware products that recycle their names regularly to create 'new' tactics to steal money from their victims, occasionally changing overall templates and some minor functions between major revisions. Windows Defence Unit belongs to one of the most prominent offshoots of this family, FakeVimes (although Windows Defence Unit is also similar to members of the FakePAV family, alternately referred to as Tritax or NameChanger), including Privacy Guard Pro, PrivacyGuard Pro 2.0, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus and Smart Security. Windows Defence Unit and its many relatives often, but not exclusively, use non-consensual installation methods or online strategies that disguise their installers as security/anti-malware downloads.
Whether Windows Defence Unit is installed through a fake security program's pop-up or other kinds of attacks, Windows Defence Unit will continue its part in this PC security hoax by pretending to be a competitive anti-malware product. While malware experts have no issues verifying that Windows Defence Unit can't identify or remove threatening software of any stripe, Windows Defence Unit will continue to pester its victims with warning messages and falsified system scan results, in an attempt to convince them otherwise. Windows Defence Unit also may use one of several methods to block other programs that Windows Defence Unit claims to be infected, with the Windows Task Manager, Registry Editor, various instant messengers and non-Internet Explorer browsers being some of its preferred targets.
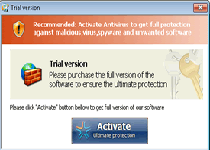
All of these functions are intended to persuade you that spending money on a premium version of Windows Defence Unit will resolve all problems and let your PC get back to normal. However, since Windows Defence Unit can only imitate any security features, money spent purchasing Windows Defence Unit will not make your PC safer than usual – although it may suppress some of Windows Defence Unit's symptoms.
Unplugging a Contrary 'Defence' Unit from Your Computer
Windows Defence Unit is no more of a defensive product for your computer than any threat would be, and its immediate removal is encouraged, both for your PC's security and to prevent you from being misled by any fake anti-malware information that's provided by Windows Defence Unit. In the case of Windows Defence Unit and other rogue anti-malware programs with long histories for blocking 'competing' products, malware experts have found the best results by disabling Windows Defence Unit before uninstalling Windows Defence Unit. Loading a backup OS from a USB peripheral and then booting into it should avoid Windows Defence Unit's Registry-based startup exploit, which is specific to the native OS.
Legitimate anti-malware products should be capable of removing Windows Defence Unit, but the rapid update cycles of its family may require that any anti-malware scanners you use also be armed with their latest updates. On the other side of the Windows Defence Unit campaign, you also should look into keeping Windows Defence Unit from seeing your hard drive at all. Web browser security protocols like disabling scripts and avoiding illegal websites will reduce your chances of contact with what malware experts have found to be the most common infection vectors for Windows Defence Unit and identical types of fake anti-malware products.

Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%AppData%\svc-weem.exe
File name: svc-weem.exeSize: 1.32 MB (1325056 bytes)
MD5: 533f55c3a8794ce722caf73d94414bb0
Detection count: 55
File type: Executable File
Mime Type: unknown/exe
Path: %AppData%
Group: Malware file
Last Updated: January 8, 2020
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.