Windows Processes Accelerator
Posted: April 7, 2012
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 2/10 |
|---|---|
| Infected PCs: | 61 |
| First Seen: | April 7, 2012 |
|---|---|
| Last Seen: | October 13, 2024 |
| OS(es) Affected: | Windows |
 Windows Processes Accelerator may market itself as an anti-virus scanner and general purpose fine-tuning utility to enhance your PC's performance, but the only working functions that Windows Processes Accelerator contains will cause the exact opposite of the desired results. With a full complement of attacks like search engine redirects and application-blocking behavior to support its fake security scam, Windows Processes Accelerator is rated by SpywareRemove.com malware researchers as a direct danger to your computer's security, in addition to being a general annoyance. Like other forms of malicious software that alter Windows components, Windows Processes Accelerator should be removed by suitable anti-malware products whenever possible, and it's strongly encouraged for you to take that action to preserve your PC instead of throwing money at Windows Processes Accelerator's online registration process.
Windows Processes Accelerator may market itself as an anti-virus scanner and general purpose fine-tuning utility to enhance your PC's performance, but the only working functions that Windows Processes Accelerator contains will cause the exact opposite of the desired results. With a full complement of attacks like search engine redirects and application-blocking behavior to support its fake security scam, Windows Processes Accelerator is rated by SpywareRemove.com malware researchers as a direct danger to your computer's security, in addition to being a general annoyance. Like other forms of malicious software that alter Windows components, Windows Processes Accelerator should be removed by suitable anti-malware products whenever possible, and it's strongly encouraged for you to take that action to preserve your PC instead of throwing money at Windows Processes Accelerator's online registration process.
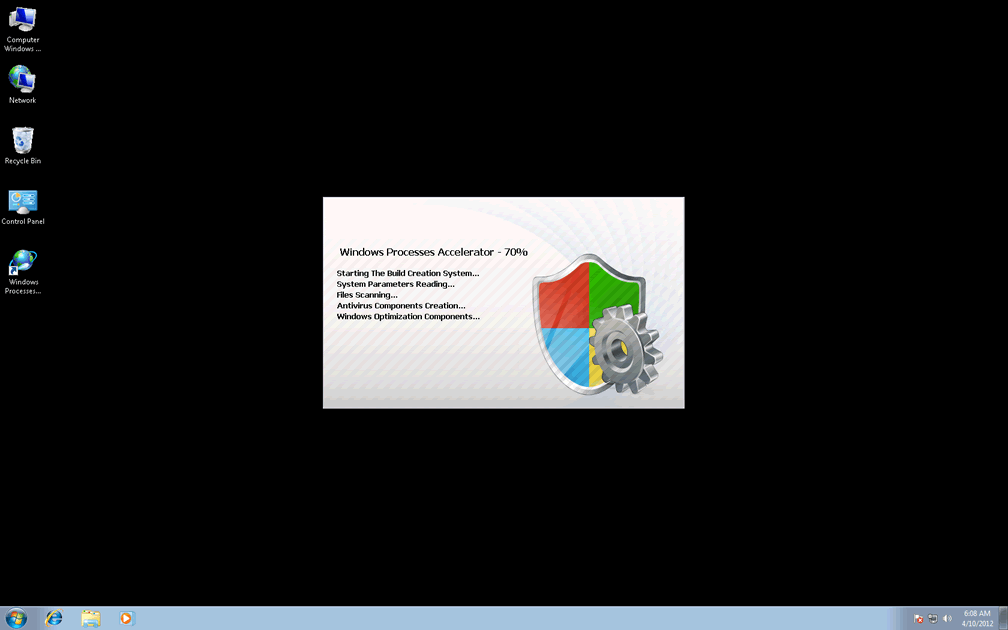
Windows Processes Accelerator – Fraudulent Software That Imitates the Real Thing to Get at Your Cash
Windows Processes Accelerator, like other rogue anti-virus programs from the FakeVimes, can be utilized to attack your web browser and security-related software, but Windows Processes Accelerator's main goal is simply to convince you that it's a 'real' anti-virus and security program. To accomplish this, Windows Processes Accelerator is often installed by fake online scanners that warn you about nonexistent PC threats on your computer, with Windows Processes Accelerator carrying on in this ignominious tradition by displaying its own fake alerts. SpywareRemove.com malware research team is comfortable in advising you always to ignore popups, scans and other forms of system analyses from Windows Processes Accelerator, which can lead you to harm your computer if you follow its recommendations. Some of the many possibilities in Windows Processes Accelerator's roulette of fake alarms include fake warning popups, which are common to the overall Win32/FakeVimes family of scamware.
Even though SpywareRemove.com malware experts emphasis that you should never spend actual money on Windows Processes Accelerator's registration key or give its criminal company access to your financial information, in some cases, a fake registration can help to make Windows Processes Accelerator less difficult than usual to remove. Inputting the code '0W000-000B0-00T00-E0020' will accomplish this free of charge.
The Obstacle Course That Windows Processes Accelerator Puts Between You and a Safe Computer
In between its attempts to convince you to spend money on registering it, Windows Processes Accelerator will also make efforts to control your web-browsing experience and ability to use unrelated applications (especially programs that are associated with system maintenance, analysis or security). Attempting to use Task Manager while Windows Processes Accelerator is active may result in Task Manager being replaced by Windows Processes Accelerator's advanced process control, although SpywareRemove.com malware researchers note that this doesn't damage Task Manager and can be resolved by insuring that Windows Processes Accelerator is shut down first. This is recommended, in any case, to give you full access to anti-malware software that can remove Windows Processes Accelerator completely.
Windows Processes Accelerator may also redirect your browser to unusual sites or block safe websites, with the majority of its redirects taking place after you attempt to access a search engine link. Because these redirects are a result of Hosts file changes, SpywareRemove.com malware researchers mention that any browser-specific change, such as changed browser settings or using a different browser, will fail to stop Windows Processes Accelerator's redirect attacks. Similar attacks to the ones noted above can also be witnessed in Windows Process Accelerator's clones, such as Privacy Guard Pro, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security and PrivacyGuard Pro 2.0.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%AppData%\NPSWF32.dll
File name: %AppData%\NPSWF32.dllFile type: Dynamic link library
Mime Type: unknown/dll
Group: Malware file
%AppData%\result.db
File name: %AppData%\result.dbMime Type: unknown/db
Group: Malware file
%AppData%\Protector-[RANDOM 3 CHARACTERS].exe
File name: %AppData%\Protector-[RANDOM 3 CHARACTERS].exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
%CommonStartMenu%\Programs\Windows Processes Accelerator.lnk
File name: %CommonStartMenu%\Programs\Windows Processes Accelerator.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
%Desktop%\Windows Processes Accelerator.lnk
File name: %Desktop%\Windows Processes Accelerator.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
Registry Modifications
HKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableRegedit" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableRegistryTools" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableTaskMgr" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "EnableLUA" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorAdmin" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorUser" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "WarnOnHTTPSToHTTPRedirect" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings "net" = "2012-4-7_2"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings "UID" = "ahwohainwk"HKEY..\..\..\..{Subkeys}HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\dvp95.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\inetlnfo.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\advxdwin.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\aswRunDll.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\aswUpdSv.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rtvscn95.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\tds-3.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\winupdate.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ozn695m5.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\atcon.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\bidef.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\..{RunKeys}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "Inspector"
Additional Information
| # | Message |
|---|---|
| 1 | Error
Trojan activity detected. System data security is at risk. It is recommended to activate protection and run a full system scan. |
| 2 | Warning
Firewall has blocked a program from accessing the Internet C:\program files\internet explorer\iexplore.exe is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server. |
| 3 | Warning! Identity theft attempt Detected
Hidden connection IP: 58.82.12.124 Target: Your passwords for sites |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.