Windows Safety Toolkit
Posted: April 21, 2012
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 2/10 |
|---|---|
| Infected PCs: | 37 |
| First Seen: | April 21, 2012 |
|---|---|
| OS(es) Affected: | Windows |
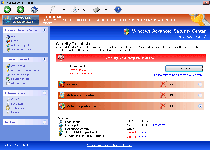 Despite its name, Windows Safety Toolkit isn't a program that's involved in any type of security-enhancing features, but rather, a rogue anti-virus product that attacks your PC's security while attempting to defraud you of your money. In accordance with its larcenous intentions, Windows Safety Toolkit will display a variety of fake warning messages to make you think that your only recourse is to buy its registration key so that Windows Safety Toolkit can delete these nonexistent PC threats. However, because Windows Safety Toolkit doesn't actually detect real attacks, infections or malicious programs, SpywareRemove.com malware experts suggest that you ignore Windows Safety Toolkit's pop-ups and remove Windows Safety Toolkit with anti-malware software, just as you would do for other members of FakeVimes. Until you've removed Windows Safety Toolkit and all related PC threats appropriately, you may also be forced to endure varied attacks, including browser hijacks and disabled security applications.
Despite its name, Windows Safety Toolkit isn't a program that's involved in any type of security-enhancing features, but rather, a rogue anti-virus product that attacks your PC's security while attempting to defraud you of your money. In accordance with its larcenous intentions, Windows Safety Toolkit will display a variety of fake warning messages to make you think that your only recourse is to buy its registration key so that Windows Safety Toolkit can delete these nonexistent PC threats. However, because Windows Safety Toolkit doesn't actually detect real attacks, infections or malicious programs, SpywareRemove.com malware experts suggest that you ignore Windows Safety Toolkit's pop-ups and remove Windows Safety Toolkit with anti-malware software, just as you would do for other members of FakeVimes. Until you've removed Windows Safety Toolkit and all related PC threats appropriately, you may also be forced to endure varied attacks, including browser hijacks and disabled security applications.
Windows Safety Toolkit – Everything That You'd Need to Keep Your PC Completely Unsafe
Windows Safety Toolkit markets itself as an anti-virus scanner with a good-sized parcel of other security features, and even includes seemingly advanced functions like phishing attack defenses, but these features are entirely fraudulent and their self-destructive advice should always be disregarded. System scans will include warnings about nonexistent infections, popup alerts will threaten you about live attacks that aren't occurring and various programs may be announced as infected. SpywareRemove.com malware experts note that the latter is particularly likely for security programs that Windows Safety Toolkit intentionally blocks (such as anti-virus scanners and Windows diagnostic applications).
Since Windows Safety Toolkit makes it difficult for you to run appropriate anti-malware programs while it's open, SpywareRemove.com malware researchers suggest that you try to launch Windows in a Windows Safety Toolkit-free boot before you try to delete Windows Safety Toolkit. Various solutions to disable Windows Safety Toolkit easily include:
- Launching Windows in Safe Mode by tapping F8 and selecting the appropriate menu option after the BIOS loads but prior to Windows loading.
- Booting Windows from a network-shared drive.
- Booting Windows from a removable drive, such as a CD or USB thumb drive.
Side Effects of Windows Safety Toolkit to Keep an Eye On
While fake pop-ups and other types of inaccurate security information are Windows Safety Toolkit's definitive symptoms, as a member of Win32/FakeVimes, Windows Safety Toolkit may also launch other attacks against your PC. Besides Windows Safety Toolkit, this family also includes such members as Privacy Guard Pro, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus, Smart Security and PrivacyGuard Pro 2.0. If desired, you can also register Windows Safety Toolkit or its relatives with the code '0W000-000B0-00T00-E0020,' as SpywareRemove.com malware analysts have found this to be occasionally useful for removing Windows Safety Toolkit and other scamware from Win32/FakeVimes.
Even though its tendency to block security programs would, by itself, be ample reason to delete Windows Safety Toolkit ASAP, Windows Safety Toolkit may also include other attacks that are characteristic of Win32/FakeVimes-based rogue AV programs. Your web browser searches may be hijacked by Hosts file changes, the Windows UAC feature may be disabled, and you may fail to receive warnings when downloading files with improper signatures. All of these attacks should be considered threats to your computer's security, and SpywareRemove.com malware experts encourage you to avoid them by deleting Windows Safety Toolkit with good anti-malware software as quickly as is convenient.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%AppData%\NPSWF32.dll
File name: %AppData%\NPSWF32.dllFile type: Dynamic link library
Mime Type: unknown/dll
Group: Malware file
%AppData%\result.db
File name: %AppData%\result.dbMime Type: unknown/db
Group: Malware file
%AppData%\W34r34mt5h21ef.dat
File name: %AppData%\W34r34mt5h21ef.datFile type: Data file
Mime Type: unknown/dat
Group: Malware file
%AppData%\Protector-[RANDOM 3 CHARACTERS].exe
File name: %AppData%\Protector-[RANDOM 3 CHARACTERS].exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
%Desktop%\Windows Safety Toolkit.lnk
File name: %Desktop%\Windows Safety Toolkit.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
%CommonStartMenu%\Programs\Windows Safety Toolkit.lnk
File name: %CommonStartMenu%\Programs\Windows Safety Toolkit.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
Registry Modifications
HKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableRegedit" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableRegistryTools" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableTaskMgr" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "WarnOnHTTPSToHTTPRedirect" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "EnableLUA" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorAdmin" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorUser" = 0HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings "UID" = "pbxqbkjqxb"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings "net" = "2012-4-21_3"HKEY..\..\..\..{Subkeys}HKEY_CURRENT_USER\Software\ASProtectHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\install[1].exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\aswRunDll.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\cmd32.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\webscanx.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\npssvc.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\scam32.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\..{RunKeys}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "Inspector"
Additional Information
| # | Message |
|---|---|
| 1 | Error
Attempt to modify Registry key entries detected. Registry entry analysis recommended. |
| 2 | Warning
Firewall has blocked a program from accessing the Internet C:\program files\internet explorer\iexplore.exe is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server. |
| 3 | Warning! Spambot detected!
Attention! A spambot sending viruses from your e-mail has been detected on your PC. |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.