Windows Warding Module
Posted: December 5, 2013
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 12 |
| First Seen: | December 5, 2013 |
|---|---|
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
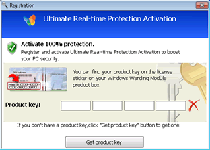
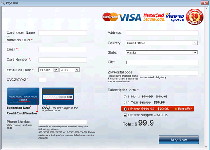
 Windows Warding Module is one of many rogue anti-malware products based on a branch of the FakeVimes family, which is known for blocking innocent programs, redirecting browsers to fake warning screens and, of course, encouraging victims to spend money on fraudulent software. Like any scamware worthy of being called such, Windows Warding Module can provide detailed, but fake system scans and multiple formats of pop-up warnings, all intended to make you buy a registration key for its full version. Also like similar scamware products, malware experts consider Windows Warding Module a high-level PC threat, and deleting Windows Warding Module with a comprehensive anti-malware product is urgently required for keeping your PC safe.
Windows Warding Module is one of many rogue anti-malware products based on a branch of the FakeVimes family, which is known for blocking innocent programs, redirecting browsers to fake warning screens and, of course, encouraging victims to spend money on fraudulent software. Like any scamware worthy of being called such, Windows Warding Module can provide detailed, but fake system scans and multiple formats of pop-up warnings, all intended to make you buy a registration key for its full version. Also like similar scamware products, malware experts consider Windows Warding Module a high-level PC threat, and deleting Windows Warding Module with a comprehensive anti-malware product is urgently required for keeping your PC safe.
How Windows Warding Module Wards You Away from Sites and Applications Alike
Based on previous generations of FakeVimes scamware like Windows Active HotSpot and Best Malware Protection, Windows Warding Module is an imitation of a real security program and may provide extensive system warnings, but no accuracy for their contents. A faux security product that's installed by separate Trojans that are specialized for distributing this family's members, Windows Warding Module's installation usually should be immediately detectable due to its pop-up alerts, offers to scan your PC and other side effects. Once it's established that all system information offered by Windows Warding Module is fake and that you never should give in to purchasing Windows Warding Module, malware analysts are mostly concerned with its security-related attacks. These attacks may consist of:
- Redirecting your browser, both to block security-oriented websites and to force your browser to load fake error pages to promote Windows Warding Module.
- Changing your browser's settings in multiple ways, most of which make your PC vulnerable to new attacks from the Web (such as other threats).
- Blocking other programs by forcing Svchost.exe (a harmless Windows executable) to launch instead. Programs blocked may include firewall utilities, Registry editors, anti-malware scanners and any number of other security tools.
All of these functions increase the susceptibility of your computer to new attacks by Windows Warding Module and other forms of risky software.
Drawing the Right Wards Between Windows Warding Module and Your System
Windows Warding Module is a dedicated fraud program that attempts to mislead its victims with as much inaccurate system data as possible, and telling the difference between an actual Windows alert and the fake warning of Windows Warding Module is useful for determining what actually is wrong with your PC. With its propensity for preventing the use of other applications that could interrupt its scam, Windows Warding Module usually will require disabling before any work towards removing Windows Warding Module can proceed. For obvious strategies useful towards this purpose, malware experts often find Safe Mode and OS-loaded USB devices to be good options.
The damage that Windows Warding Module may cause to your PC in the meantime shouldn't be taken for granted, even when you've already determined that giving Windows Warding Module money or personal information isn't in your best interests. Because of the security issues related to the habitual attacks of Windows Warding Module's family, malware researchers must recommend immediate action in all cases. This is just as applicable to other members of FakeVimes, including Privacy Guard Pro, PrivacyGuard Pro 2.0, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus and Smart Security.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:setup.exe
File name: setup.exeSize: 1.06 MB (1061216 bytes)
MD5: 96d3b1f95e3fde25ba8e8d0e62bc9d21
Detection count: 54
File type: Executable File
Mime Type: unknown/exe
Group: Malware file
Last Updated: January 8, 2020
%AppData%\result1.db
File name: %AppData%\result1.dbMime Type: unknown/db
Group: Malware file
%AppData%\guard-[RANDOM CHARACTERS].exe
File name: %AppData%\guard-[RANDOM CHARACTERS].exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
Registry Modifications
HKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon "Shell"="C:\\Users\\User\\AppData\\Roaming\\guard-[RANDOM CHARACTERS].exe"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "GuardSoftware" = "%AppData%\guard-[RANDOM CHARACTERS].exe"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes"=".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments "SaveZoneInformation"=1HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe "Debugger"="svchost.exe"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe "Debugger"="svchost.exe"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "EnableLUA" = "0"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorUser" = "0"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorAdmin" = "0"
Additional Information
| # | Message |
|---|---|
| 1 | Error Attempt to run a potentially dangerous script detected. Full system scan is highly recommended. |
| 2 | Error System data security is at risk! To prevent potential PC errors, run a full system scan. |
| 3 | Firewall has blocked a program from accessing the Internet c:\windows\system32\iexplore.exe is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server. |
| 4 | Warning! Identity theft attempt detected Hidden connection IP: xx.xxx.xxx.xxx Target: Microsoft Corporation keys Your IP: 127.0.0.1 |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.