Savings Wave
Posted: September 23, 2013
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Ranking: | 10,933 |
|---|---|
| Threat Level: | 2/10 |
| Infected PCs: | 16,364 |
| First Seen: | September 23, 2013 |
|---|---|
| Last Seen: | March 3, 2025 |
| OS(es) Affected: | Windows |
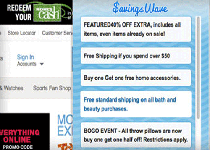 Savings Wave is an adware program that may display annoying pop-up advertisements, coupons and sponsored links via a pop-up box on Youtube, Google, Facebook, Amazon and other websites that computer users are visiting. Savings Wave pop-up ads will be displayed as boxes, which include a variety of coupons that are available or as underlined keywords, which when clicked may show an advertisement that declares it comes to target web user by Savings Wave. Savings Wave is an extension for Internet Explorer, Mozilla Firefox and Google Chrome that is usually inserted when web users install another free software products, such as video recording/streaming, download-managers or PDF creators, that had packaged into their installation Trusted Saver. When computer users install these free software products, they may also install Savings Wave. While being installed, whenever the PC user will visit Best Buy, Expedia, Facebook or any other website, Savings Wave may show a 'See Similar' button on product images, which when clicked may display pop-up ads by Savings Wave. Savings Wave may also show advertising banners on the websites that Internet user are visiting, and as they browse the web, it may display coupons and other deals available numerous websites.
Savings Wave is an adware program that may display annoying pop-up advertisements, coupons and sponsored links via a pop-up box on Youtube, Google, Facebook, Amazon and other websites that computer users are visiting. Savings Wave pop-up ads will be displayed as boxes, which include a variety of coupons that are available or as underlined keywords, which when clicked may show an advertisement that declares it comes to target web user by Savings Wave. Savings Wave is an extension for Internet Explorer, Mozilla Firefox and Google Chrome that is usually inserted when web users install another free software products, such as video recording/streaming, download-managers or PDF creators, that had packaged into their installation Trusted Saver. When computer users install these free software products, they may also install Savings Wave. While being installed, whenever the PC user will visit Best Buy, Expedia, Facebook or any other website, Savings Wave may show a 'See Similar' button on product images, which when clicked may display pop-up ads by Savings Wave. Savings Wave may also show advertising banners on the websites that Internet user are visiting, and as they browse the web, it may display coupons and other deals available numerous websites.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%PROGRAMFILES%\Savings Wave Plugin\Savings Wave Plugin-bho.dll
File name: Savings Wave Plugin-bho.dllSize: 748.03 KB (748032 bytes)
MD5: 22ac0307c594a9d3088aca0fb29d538b
Detection count: 3,958
File type: Dynamic link library
Mime Type: unknown/dll
Path: %PROGRAMFILES%\Savings Wave Plugin
Group: Malware file
Last Updated: October 7, 2020
%PROGRAMFILES%\Savings Wave\Savings Wave-bho.dll
File name: Savings Wave-bho.dllSize: 602.5 KB (602504 bytes)
MD5: 1e1fb3d9b4d3d468eb0e4079ced1c659
Detection count: 230
File type: Dynamic link library
Mime Type: unknown/dll
Path: %PROGRAMFILES%\Savings Wave
Group: Malware file
Last Updated: June 5, 2014
%PROGRAMFILES(x86)%\Savings Wave\FrameworkBHO64.dll
File name: FrameworkBHO64.dllSize: 492.63 KB (492632 bytes)
MD5: d70dcf6d32164f10da61f06e496b35b1
Detection count: 26
File type: Dynamic link library
Mime Type: unknown/dll
Path: %PROGRAMFILES(x86)%\Savings Wave
Group: Malware file
Last Updated: June 5, 2014
%PROGRAMFILES%\Savings Wave\FrameworkBHO.dll
File name: FrameworkBHO.dllSize: 258.08 KB (258088 bytes)
MD5: 8f46f03a3969be8e533dd8b094853b69
Detection count: 20
File type: Dynamic link library
Mime Type: unknown/dll
Path: %PROGRAMFILES%\Savings Wave
Group: Malware file
Last Updated: June 5, 2014
%PROGRAMFILES%\savings wave\savings wave-bg.exe
File name: savings wave-bg.exeSize: 742.28 KB (742280 bytes)
MD5: 9e16a803d4584761c3cec835fdfa0bca
Detection count: 9
File type: Executable File
Mime Type: unknown/exe
Path: %PROGRAMFILES%\savings wave
Group: Malware file
Last Updated: June 5, 2014
%TEMP%\setup_savings wave-1.0.20140221.exe
File name: setup_savings wave-1.0.20140221.exeSize: 496.82 KB (496824 bytes)
MD5: b9b1f87dffafd4d97601a1b9813a291c
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %TEMP%
Group: Malware file
Last Updated: June 5, 2014
%PROGRAMFILES(x86)%\Savings Wave\Savings Wave-updater.exe
File name: Savings Wave-updater.exeSize: 384.39 KB (384392 bytes)
MD5: f3f4ba02aa343db22d6c8c890045b2df
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %PROGRAMFILES(x86)%\Savings Wave
Group: Malware file
Last Updated: June 6, 2014
More files
Registry Modifications
CLSID{11111111-1111-1111-1111-110111271165}{1DB0B3DE-46A7-4BD1-BE99-79BA4441B56C}{22222222-2222-2222-2222-220122272265}{44444444-4444-4444-4444-440144274465}{55555555-5555-5555-5555-550155275565}{587D9DE0-E7BD-403C-85C9-18C6E74CCA6F}{66666666-6666-6666-6666-660166276665}{711BC232-43EE-4460-9F5F-3E5A46182646}{71ADC26E-438C-4450-BEBF-145AFD188246}{B313DEAE-5D45-48B8-9FF5-DA7428A96101}{B320DE57-5D61-487F-B689-D074B7A93901}{FDE634B1-36EE-4A17-9BDD-DDEFE9B6707E}{FDE7341D-3650-4ACF-8498-4CEFE8B6EA7E}HKEY..\..\..\..{RegistryKeys}Software\AppDataLow\Software\Crossrider\onBeforeNavigate\12765Software\AppDataLow\Software\Crossrider\onRequest\12765Software\AppDataLow\Software\Savings WaveSOFTWARE\Classes\CrossriderApp0012765.BHOSOFTWARE\Classes\CrossriderApp0012765.BHO.1SOFTWARE\Classes\CrossriderApp0012765.SandboxSOFTWARE\Classes\CrossriderApp0012765.Sandbox.1Software\InstalledBrowserExtensions\Innovative Apps\12765Software\Microsoft\Internet Explorer\Approved Extensions\{11111111-1111-1111-1111-110111271165}SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{1DB0B3DE-46A7-4BD1-BE99-79BA4441B56C}SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{11111111-1111-1111-1111-110111271165}Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{11111111-1111-1111-1111-110111271165}Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{FDE634B1-36EE-4A17-9BDD-DDEFE9B6707E}Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{11111111-1111-1111-1111-110111271165}Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{FDE634B1-36EE-4A17-9BDD-DDEFE9B6707E}SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce\Savings Wave-repairJobSoftware\Proxy\installations\Savings WaveSOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{1DB0B3DE-46A7-4BD1-BE99-79BA4441B56C}SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\explorer\Browser Helper Objects\{11111111-1111-1111-1111-110111271165}SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\RunOnce\Savings Wave-repairJobSOFTWARE\Wow6432Node\Proxy\Installations\Savings WaveSOFTWARE\Wow6432Node\Savings WaveHKEY_LOCAL_MACHINE\Software\[APPLICATION]\Microsoft\Windows\CurrentVersion\Uninstall..{Uninstaller}35939_Savings WaveSavings Wave
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.