Troj/Agent-YDC
Posted: October 9, 2012
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 9/10 |
|---|---|
| Infected PCs: | 37 |
| First Seen: | October 9, 2012 |
|---|---|
| Last Seen: | February 2, 2021 |
| OS(es) Affected: | Windows |
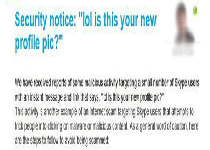 Troj/Agent-YDC is one of two variants of the Dorkbot worm that have been noted for their distribution through Skype spam messages. While the messages linking to Troj/Agent-YDC claim to be linking to a personal picture, the .zip archive installs either Troj/Agent-YDC or Troj/Agent-YCW, which will then open a backdoor on your computer. This backdoor allows criminals to engage in additional attacks through a remote server. SpywareRemove.com malware researchers have two primary pieces of advice for potential victims of Troj/Agent-YDC attacks: avoid suspicious links and scan your computer after any contact with files that are reminiscent of the description noted above. Along with all these warnings, victims of Troj/Agent-YDC attacks also should be aware that Troj/Agent-YDC, like any variant of Dorkbot, can abuse USB ports for its own distribution. Using anti-malware scanners to delete copies of Troj/Agent-YDC from any removable device is, therefore, just as necessary as deleting Troj/Agent-YDC from your primary hard drives.
Troj/Agent-YDC is one of two variants of the Dorkbot worm that have been noted for their distribution through Skype spam messages. While the messages linking to Troj/Agent-YDC claim to be linking to a personal picture, the .zip archive installs either Troj/Agent-YDC or Troj/Agent-YCW, which will then open a backdoor on your computer. This backdoor allows criminals to engage in additional attacks through a remote server. SpywareRemove.com malware researchers have two primary pieces of advice for potential victims of Troj/Agent-YDC attacks: avoid suspicious links and scan your computer after any contact with files that are reminiscent of the description noted above. Along with all these warnings, victims of Troj/Agent-YDC attacks also should be aware that Troj/Agent-YDC, like any variant of Dorkbot, can abuse USB ports for its own distribution. Using anti-malware scanners to delete copies of Troj/Agent-YDC from any removable device is, therefore, just as necessary as deleting Troj/Agent-YDC from your primary hard drives.
Troj/Agent-YDC and the New Narcissus Trap
Troj/Agent-YDC and Troj/Agent-YCW are Dorkbot variants that have taken up a new means of distribution: instant messages that pretend to offer links to pictures. Current templates that SpywareRemove.com malware experts have surveyed attempt to exhibit links to Troj/Agent-YDC as pictures of the person that's being targeted – thus tempting them into trusting a link in hopes of seeing something interesting about themselves. However, instead of their own faces being revealed in a JPG or GIF, the corresponding zip file will install Troj/Agent-YDC or Troj/Agent-YCW (which are identified as separate but closely-related variants of the Dorkbot worm).
After exploiting the victim's vanity for its own benefit, Troj/Agent-YDC creates a backdoor that lets Troj/Agent-YDC contact a C&C serve. This server is then used to conduct other attacks, including the installation of other PC threats, disabling security features, using the infected PC for botnet attacks or stealing personal information. SpywareRemove.com malware researchers note that any type of malware capable of backdoor attacks such as Troj/Agent-YDC should be considered a high-level security risk to be deleted as quickly as you can access any appropriate anti-malware programs.
Troj/Agent-YDC's Backup Transportation Routes
SpywareRemove.com malware researchers have found that Troj/Agent-YDC also can be spread through other means besides the one noted above. These secondary paths for infection by Troj/Agent-YDC should be taken into account when removing Troj/Agent-YDC from your computer – lest Troj/Agent-YDC spread to other PCs in the vicinity:
- USB drives. Troj/Agent-YDC may copy itself to removable USB devices and then install itself on any computer that plugs in the infected device.
- Other instant messaging platforms, including IRC, Windows Live Messenger and Pidgin (amongst others).
- Social networking sites, of which the most prominent are Facebook and Twitter.
Any anti-malware scans for detecting and removing Troj/Agent-YDC should, naturally, also be used to cover removable devices and other vulnerable areas of your PC.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%PROFILE%\Application Data\Jqfsfb.exe
File name: %PROFILE%\Application Data\Jqfsfb.exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
skype_06102012_image.zip
File name: skype_06102012_image.zipMime Type: unknown/zip
Group: Malware file
skype_08102012_image.zip
File name: skype_08102012_image.zipMime Type: unknown/zip
Group: Malware file
Registry Modifications
HKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "Skype " = "C:\Documents and Settings\support\Application Data\Jqfsfb.exe"
Additional Information
| # | Message |
|---|---|
| 1 | lol is this your new profile pic? http://goo.gl/[REDACTED]?img=[USERNAME] |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.