Trojan.Maljava.B
Posted: March 4, 2013
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 9/10 |
|---|---|
| Infected PCs: | 44 |
| First Seen: | March 4, 2013 |
|---|---|
| Last Seen: | November 1, 2022 |
| OS(es) Affected: | Windows |
Trojan.Maljava.B is one of two Trojan droppers that have been involved in the distribution of Trojan.Naid, a backdoor Trojan that allows criminals to access the compromised PCs. While Naid attacks have, so far, been limited to targeting industrial victims for the purposes of stealing confidential industry information, SpywareRemove.com malware experts warn that exposure to websites that host Trojan.Maljava.B-based drive-by-downloads can compromise most Windows PCs – as long as they're using a vulnerable version of Java. Disabling Java and using other browser-related security methods can block a Trojan.Maljava.B attack, but if Trojan.Maljava.B has succeeded in infecting your PC, you should turn to a robust anti-malware program to remove Trojan.Maljava.B's payloads safely.
How Trojan.Maljava.B Gets the Malware Ball Rolling
Trojan.Maljava.B usually is used to deliver complex, multi-stage attacks to the compromised PC, but requires that your PC be exposed toTrojan.Maljava.B first. As a Java-based Trojan, Trojan.Maljava.B usually is embedded in a malicious website, after which Trojan.Maljava.B can launch (without symptoms) as soon as your browser loads the site. For this reason, SpywareRemove.com malware experts tend to recommend disabling Java and other exploitable browser features whenever you're loading a site that isn't completely trustworthy. In some cases, patching Java may allow you to block attacks like Trojan.Maljava.B's own, but Trojan.Maljava.B also has been known to use zero-day exploits that can't be thwarted via security patches.
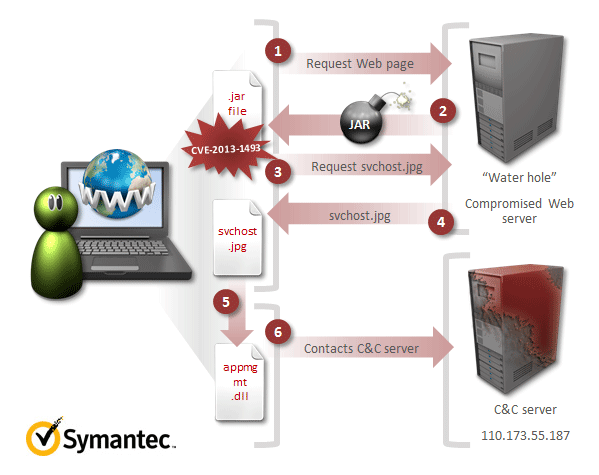
Trojan.Maljava.B's most well-recorded use involves the launch of a second Trojan, the appropriately-named Trojan.Dropper (that's disguised as a fake JPG image). This dropper installs the final payload, Trojan.Naid. Trojan.Naid creates a backdoor connection that enables criminals to have a high degree of access to your PC, as well as control over its basic functions. Through Trojan.Maljava.B's payload, therefore, criminals may choose to steal your personal information, delete files, install other malware or change system settings on a whim.
Keeping Trojan.Maljava.B from Using Java to Pry Open Your PC
As mentioned earlier, disabling Java will prevent Trojan.Maljava.B from enacting the exploit that Trojan.Maljava.B uses to attack your computer. SpywareRemove.com malware experts also have noted that Trojan.Maljava.B and related PC threats all are limited to Windows operating systems, which makes Mac and Unix-based computers safe from Trojan.Maljava.B by default.
Since Trojan.Maljava.B requires you to be exposed to a malicious or hacked site before Trojan.Maljava.B can attack your computer, you should take care to avoid potential redirects to Trojan.Maljava.B-hosting sites. E-mail spam is an especially-prominent infection vector for industrial saboteurs like Trojan.Naid, and SpywareRemove.com malware researchers warn that such messages are likely to be designed to look like they're relevant to the victim's business.
Having any motive to think that Trojan.Maljava.B may have attacked your PC, anti-malware software should be used to remove Trojan.Maljava.B's payload as accurately as possible. There are no symptoms of either Trojan.Maljava.B's attack or Trojan.Naid's attacks, and you never should expect to be able to detect similar high-level PC threats visually.
Figure 1. Diagram and anatomy of Java Zero-Day Attack related to Trojan.Maljava.B - Source: Symantec
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.