Win32/Criakl.C
Posted: January 5, 2015
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 9/10 |
|---|---|
| Infected PCs: | 101 |
| First Seen: | January 5, 2015 |
|---|---|
| Last Seen: | March 6, 2024 |
| OS(es) Affected: | Windows |
 Win32/Criakl.C is a member of a family of Trojans that conduct ransomware-themed attacks against your PC, such as encrypting files or locking your OS while demanding a fee. Because Win32/Criakl.C was identified late in 2014, the extent of its capabilities and associations with other Criakl Trojans has yet to be fully revealed. However, Win32/Criakl.C always should be assumed to be threatening and a risk to the safety of your computer. You should resolve attacks symptomatic of Win32/Criakl.C or other Criakl family members with dedicated anti-malware scans of your PC, which can delete Win32/Criakl.C and put you in a position to restore any lost data.
Win32/Criakl.C is a member of a family of Trojans that conduct ransomware-themed attacks against your PC, such as encrypting files or locking your OS while demanding a fee. Because Win32/Criakl.C was identified late in 2014, the extent of its capabilities and associations with other Criakl Trojans has yet to be fully revealed. However, Win32/Criakl.C always should be assumed to be threatening and a risk to the safety of your computer. You should resolve attacks symptomatic of Win32/Criakl.C or other Criakl family members with dedicated anti-malware scans of your PC, which can delete Win32/Criakl.C and put you in a position to restore any lost data.
The Trojans that Take Your Files before Taking Your Money
The Win32/Criakl.C's family, also referred to by aliases including Cryakl and Filecoder, includes attacks typical of some variants of ransomware, especially file encrypting Trojans. The relative newness of the Win32/Criakl family has resulted in limited sample availability, and Win32/Criakl.C may be a party to additional attacks beyond those listed here. However, its primary symptoms tend to consist of the following functions:
- Win32/Criakl.C will set itself to launch automatically during the Windows startup routine, making itself active as a passive background process or, in some cases, code that injects into a preexisting process.
- Win32/Criakl.C may open up network communications with a C&C server. Such servers may allow Trojans to install updates, upload information from your system, download other threats or reconfigure their attacks as per their received instructions.
- Win32/Criakl.C may encrypt files on your PC, particularly files with major media and text formats, such as BMP or DOC. Data encryption can prevent you from opening or using the affected files, although some third parties do provide utilities that can offer limited encryption reversal features.
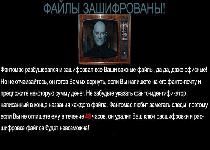
- Win32/Criakl.C will display a warning message that recommends paying its ransom fee as a solution to the above attack. Because of the inherent dangers of transferring money or information to third parties, malware analysts advise against using this course of action for reversing the consequences of a Win32/Criakl.C infection.
Bailing Yourself out of the Latest Ransomware Family's Ransom
Win32/Criakl.C and other file encryptor Trojans require your acquiescence to receive their ransom funds. However, conventional means of backing your files up can help you circumvent most file-encrypting attacks. For maximum safety from threats like Win32/Criakl.C, malware researchers particularly encourage using backups stored in remote, safe locations. USB peripherals and cloud storage services are two of the many alternatives for storing your files safely.
Win32/Criakl.C may provide its instructions in formats meant to imitate legal alerts or use other strategies to lure its victims. However, you always should be able to identify Win32/Criakl.C and other, threatening software through their recommended payment methods, which may include such unorthodox services as the Tor browser or Ukash. While you may be unable to access your files or major OS features with Win32/Criakl.C active, appropriate anti-malware products and strategies should enable Win32/Criakl.C's simple deletion.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:C:\Users\<username>\downloads\p1os9e6mvu.exe
File name: C:\Users\<username>\downloads\p1os9e6mvu.exeMD5: 572f82d2b1ffeb26681328e7c78a9528
File type: Executable File
Mime Type: unknown/exe
Group: Malware file
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.