KEYHolder Ransomware
Posted: December 12, 2014
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 33 |
| First Seen: | December 12, 2014 |
|---|---|
| Last Seen: | April 2, 2020 |
| OS(es) Affected: | Windows |
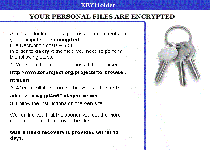 The KEYHolder Ransomware is a file encryptor Trojan that makes popular formats of files on your PC unreadable, and then requests a ransom fee to restore them back to normal. As usual for such attacks, paying the five hundred USD price demanded by the KEYHolder Ransomware is unnecessary for restoring your files, assuming the presence of appropriate anti-malware solutions and good file backup protocols. However, the KEYHolder Ransomware may interfere with the System Restore feature and be responsible for other security risks until you can remove the KEYHolder Ransomware from your PC.
The KEYHolder Ransomware is a file encryptor Trojan that makes popular formats of files on your PC unreadable, and then requests a ransom fee to restore them back to normal. As usual for such attacks, paying the five hundred USD price demanded by the KEYHolder Ransomware is unnecessary for restoring your files, assuming the presence of appropriate anti-malware solutions and good file backup protocols. However, the KEYHolder Ransomware may interfere with the System Restore feature and be responsible for other security risks until you can remove the KEYHolder Ransomware from your PC.
The File Locker Hiding Behind an Onion Browser
The KEYHolder Ransomware may be in distribution in the wild, but recently was associated with e-mail campaigns targeting various US-based company networks. In addition to infecting the initially compromised PCs, the KEYHolder Ransomware also attacked local network-linked machines. Current evidence leads malware experts to suspect that the latter attacks are based on a backdoor exploit allowing third parties to issue direct instructions to the KEYHolder Ransomware, as opposed to an automatic, worm-based infection method.
The KEYHolder Ransomware targets popular file formats for images, audio files and documents, encrypting them to make them temporarily unreadable. Unusually, the modified files don't have their file names changed, which could make it difficult to identify the KEYHolder Ransomware-affected files without opening each one individually. These modifications may not affect all files of a given format, and the KEYHolder Ransomware has been seen targeting the contents of certain folders, such as My Documents, specifically.
In addition to its file encrypting attack, the KEYHolder Ransomware also provides instructions in text and image formats supposedly for decrypting your data. The KEYHolder Ransomware recommends your use of Tor, an anonymity-enabling browser, to pay a fee for recovering your information from its attacks. As always, there are no meaningful guarantees that the KEYHolder Ransomware's maintainers will provide any decryption solutions afterward, and you should take any promises this threatening software makes with a large grain of salt.
Holding the Keys to Your Escape from File Encrypting Attacks
Along with fraudulent e-mail messages, the KEYHolder Ransomware also has been confirmed to use specially modified versions of Adobe Flash installers as ways to infect new PCs. Outdated JavaScript also is an estimated instigator of the KEYHolder Ransomware infections due to the accompanying vulnerabilities that could allow attacks. PC users, both personal and professional, that may be victims of the KEYHolder Ransomware attacks also should monitor their local network security, thereby preventing the KEYHolder Ransomware from encrypting files for other systems on the same network.
Paying a KEYHolder Ransomware's fee may or may not give you access to new solutions to save your files, but malware experts recommend restoring them from a remote backup, as the cheapest alternative. Anti-malware tools can, as always, be helpful in removing the KEYHolder Ransomware, although file decryption typically requires specialized tools. Due to the recent identification of the KEYHolder Ransomware, its limited samples and restricted distribution, malware experts have yet to find any functional decryption tools made available by third parties. Thus, prevention continues to be the ideal defense against the KEYHolder Ransomware and similar threats.
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.