Windows Protection Booster
Posted: March 5, 2014
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 26 |
| First Seen: | March 5, 2014 |
|---|---|
| Last Seen: | March 11, 2021 |
| OS(es) Affected: | Windows |
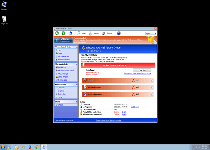
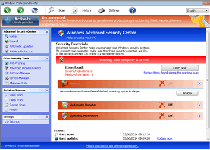
 Windows Protection Booster is a rogue anti-malware product that provides fake threat-detection functions meant to encourage the purchase of its full version, which Windows Protection Booster claims has the ability to remove all detected threats. Unlike any legitimate anti-malware program, Windows Protection Booster has an extensive background that outlines back through prominent families of nearly-identical scamware and is completely incapable of protecting your PC from real infections. Because malware experts have noted security issues with Windows Protection Booster that make Windows Protection Booster an active threat to your computer, you always should act to remove Windows Protection Booster as soon as you can.
Windows Protection Booster is a rogue anti-malware product that provides fake threat-detection functions meant to encourage the purchase of its full version, which Windows Protection Booster claims has the ability to remove all detected threats. Unlike any legitimate anti-malware program, Windows Protection Booster has an extensive background that outlines back through prominent families of nearly-identical scamware and is completely incapable of protecting your PC from real infections. Because malware experts have noted security issues with Windows Protection Booster that make Windows Protection Booster an active threat to your computer, you always should act to remove Windows Protection Booster as soon as you can.
The Fake Protection You may Know by Another Name
Windows Protection Booster is a clone of other scamware products that try to acquire money by pretending to have features that they don't possess. Past research by malware experts has associated Windows Protection Booster and its army of clones with the Tritax and FakePAV families, although they also bear a strong resemblance to at least one recent branch of FakeVimes. All of these PC threats are classified as threats, both for their fraudulent marketing methods, and for additional attacks that endanger your PC. Some examples of Windows Protection Booster's clones are Privacy Guard Pro, PrivacyGuard Pro 2.0, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus and Smart Security.
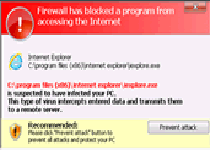
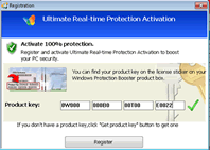
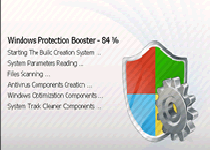
Unlike spyware and other, subversive PC threats, Windows Protection Booster isn't difficult to identify; once Windows Protection Booster is installed, Windows Protection Booster loads a fake system scanner that launches whenever Windows starts. This scanner component will pretend to detect sophisticated threats – and in the meantime, Windows Protection Booster also displays various pop-up warning messages. Windows Protection Booster's warnings may imitate firewalls and other security utilities, and may claim to be protecting you from infected software.
Nonetheless, despite the potential disruption caused by these functions, malware researchers found more reason to be concerned with Windows Protection Booster through its trend of blocking other software. These attacks may go through the Registry's settings, or they may involve monitoring your active memory processes so that Windows Protection Booster can automatically terminate 'blacklisted' ones, such as Firefox, Yahoo Messenger or Task Manager. Your access to basic security software usually will be denied, as long as Windows Protection Booster is open.
Saving Your Computer from the Protection that Means nothing But Ill Will
As long as you don't mistake Windows Protection Booster for a real security program, Windows Protection Booster isn't a danger to your wallet, but its simple presence on your computer will block your access to security software and other programs. Unsurprisingly, malware researchers recommend dealing with this promptly by using any methods required to block Windows Protection Booster from launching, which will let your anti-malware programs proceed with removing Windows Protection Booster, unimpeded. Restarting your computer and tapping F8 till you can access Safe Mode from the relevant menu should allow you a sufficiently secure environment for scanning your PC.
Windows Protection Booster and its kin have a heavy, but not exclusive reliance on compromised websites and advertisements for their distribution. These online attacks may claim that your computer has been compromised or that it requires an update. Blocking scripts by default and having a good online security program are some of the solutions malware analysts would recommend for avoiding Windows Protection Booster-installing attacks.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:svc-kasc.exe
File name: svc-kasc.exeSize: 1.05 MB (1055232 bytes)
MD5: 9b5dc03ebf5b29736a0dc22b9755cfcb
Detection count: 11
File type: Executable File
Mime Type: unknown/exe
Group: Malware file
Last Updated: January 8, 2020
%AppData%\data.sec
File name: %AppData%\data.secMime Type: unknown/sec
Group: Malware file
%AppData%\svc-[RANDOM CHARACTERS].exe
File name: %AppData%\svc-[RANDOM CHARACTERS].exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
%AllUsersProfile%\Start Menu\Programs\Windows Protection Booster.lnk
File name: %AllUsersProfile%\Start Menu\Programs\Windows Protection Booster.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
%UserProfile%\Desktop\Windows Protection Booster.lnk
File name: %UserProfile%\Desktop\Windows Protection Booster.lnkFile type: Shortcut
Mime Type: unknown/lnk
Group: Malware file
Registry Modifications
File name without pathWindows Protection Booster.lnkHKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "S_SC" = %AppData%\svc-[RANDOM CHARACTERS].exeHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "ZSFT" = %AppData%\svc-[RANDOM CHARACTERS].exeHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "MS-SEC" = %AppData%\svc-[RANDOM CHARACTERS].exeHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes" = ".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;"HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments "SaveZoneInformation" = 1HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon "Shell" = "%AppData%\svc-[RANDOM CHARACTERS].exe"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorAdmin" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "ConsentPromptBehaviorUser" = 0HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\bckd "ImagePath" = 22.sys HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "EnableLUA" = 0HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "EnableVirtualization" = 0HKEY..\..\..\..{Subkeys}HKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exeHKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exeHKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exeHKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exeHKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpCmdRun.exeHKEY_LOCAL_MACHINE\software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exeHKEY_LOCAL_MACHINE\Software\microsoft\Windows NT\CurrentVersion\Image File Execution Options\k9filter.exe
Additional Information
| # | Message |
|---|---|
| 1 | Error System data security is at risk! To prevent potential PC errors, run a full system scan. |
| 2 | Error Trojan activity detected. System integrity at risk. Full system scan is highly recommended. |
| 3 | Firewall has blocked a program from accessing the Internet Internet Explorer C:\Windows\system32\iexplore.exe is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server.ran |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.