Troldesh Ransomware
Posted: June 3, 2015
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 26 |
| First Seen: | June 3, 2015 |
|---|---|
| Last Seen: | June 16, 2020 |
| OS(es) Affected: | Windows |
 The Troldesh Ransomware is a file encryption Trojan that modifies the personal data of your computer as a preliminary to holding it for ransom. After its initial attacks, the Troldesh Ransomware also displays telltale ransom messages and other, readily visible symptoms, including a request to open direct, e-mail communication with its developers. However, there is a degree of inherent unreliability in purchasing decryption services from the persons responsible for the original attacks. As a result, malware experts discourage it, instead recommending using anti-malware products for deleting the Troldesh Ransomware, along with typical file backup strategies.
The Troldesh Ransomware is a file encryption Trojan that modifies the personal data of your computer as a preliminary to holding it for ransom. After its initial attacks, the Troldesh Ransomware also displays telltale ransom messages and other, readily visible symptoms, including a request to open direct, e-mail communication with its developers. However, there is a degree of inherent unreliability in purchasing decryption services from the persons responsible for the original attacks. As a result, malware experts discourage it, instead recommending using anti-malware products for deleting the Troldesh Ransomware, along with typical file backup strategies.
An Open Conversation with Ransomware Admins
The Troldesh Ransomware is a Russia-based Trojan that also includes functions intended for targeting English-speaking victims, with e-mail spam serving as its current mode of public distribution. Opening the accompanying threatening file attachments installs the Troldesh Ransomware onto the compromised PC, allowing the Troldesh Ransomware to scan your hard drive for personal files (such as pictures, audio or spreadsheets). The Troldesh Ransomware then encrypts them, rearranging the internal data of the files so that they're unreadable. The Troldesh Ransomware includes a file renaming function that could make it difficult to identify any individual files. However, malware experts have noted that all affected files can be found broadly via the use of the '=.xtbl' suffix.
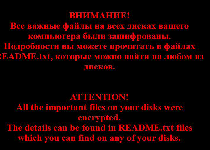
After attacking your files, the Troldesh Ransomware displays a dual English-Russian warning message that redirects you to any of its multiple, instructional text files. The contents of these instructions provide the Troldesh Ransomware's most noteworthy divergence from file encryptors like the Critoni Ransomware: The Troldesh Ransomware requests that the victim make personal, e-mail-based contact with its perpetrators. Previously, malware experts have seen most communication methods using automated forms and payment methods, such as Ukash and Web pages designed for the Tor browser.
Unsurprisingly, the ensuing conversations include the same, ultimate consequences seen in other attacks. The Troldesh Ransomware's admins demand the payment of a triple digit ransom (although they can, in theory, be bargained down) in exchange for the decryption of your personal files. They also offer to decrypt one file for free, along with implementing a strict time limit for the payment.
Keeping a File Hostage Situation from Turning Lethal
Prior communications with the Troldesh Ransomware's administrators have led to fee demands of nearly 300 USD, regardless of the types of personal content being encrypted. Furthermore, there are no guarantees of any additional file encryption following after a victim's payment of this ransom, which is one reason malware experts don't recommend it. Remote file backups, such as using a 'cloud' storage server, can provide robust protection from attacks like the Troldesh Ransomware's payload, which limits its file-encrypting scans to your PC's personal hard drive.
No matter if you choose or not to do anything to recover your files, deleting the Troldesh Ransomware, like all threats, should use dedicated anti-malware tools whenever possible. While symptoms of a Troldesh Ransomware infection should be relatively straightforward to notice, prevention can save your files from unnecessary harm. Scanning e-mail attachments that you don't trust implicitly is one of the quickest ways to keep a would-be Trojan dropper from installing Trojans like the Troldesh Ransomware.
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.