XRTN Ransomware
Posted: December 17, 2015
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 8/10 |
|---|---|
| Infected PCs: | 21 |
| First Seen: | December 17, 2015 |
|---|---|
| Last Seen: | May 6, 2024 |
| OS(es) Affected: | Windows |
 The XRTN Ransomware is a file encryptor: a Trojan that encodes your files in such a way as to prevent them from opening. Like the great majority of past file encryptors, the XRTN Ransomware accompanies its attacks with messages instructing its victims to contact an e-mail address for instructions on ransoming their files back to normal. Because of the unreliability of such methods, malware analysts deem keeping remote file backups and using anti-malware products for uninstalling the XRTN Ransomware to be the superior solution.
The XRTN Ransomware is a file encryptor: a Trojan that encodes your files in such a way as to prevent them from opening. Like the great majority of past file encryptors, the XRTN Ransomware accompanies its attacks with messages instructing its victims to contact an e-mail address for instructions on ransoming their files back to normal. Because of the unreliability of such methods, malware analysts deem keeping remote file backups and using anti-malware products for uninstalling the XRTN Ransomware to be the superior solution.
The Key to Your Files that the XRTN Ransomware Locks Away
The XRTN Ransomware is a threat based on a previous family, VaultCrypt, and like that threat uses a combination of free software and batch files to attack an infected computer. Unlike its recent ancestor, the XRTN Ransomware also includes the launching of a Word document in its basic payload, which has caused some sources to speculate that the XRTN Ransomware is distributing itself through e-mail Word attachments. However, any included documentation is secondary to the XRTN Ransomware's primary purpose of encrypting your files.
A batch file components combined with Gnu Privacy Guard (a non-malicious file encryption tool) allow the XRTN Ransomware to encrypt files of specific types with an RSA-1024 algorithm after the Trojan takes further steps for concealing the resultant decryption key from the user. The effect is that all targeted files are made effectively unreadable and unrecoverable. Examples of significant file types targeted by current versions of the XRTN Ransomware include:
- Word documents, including .DOC and .DOCX.
- Adobe .PDF files.
- .ZIP archives.
- Image files, such as JPGs.
- Excel spreadsheets, such as .XLS and .XLSX.
Other file types also are supported, with an emphasis on spreadsheets, CD storage, CAD files and general databases. Although the XRTN Ransomware stores its decryption key file locally, it also is encrypted and requires a secondary key possessed by the threat's administrator.
The Least Costly Recovery Option Against an XRTN Ransomware Attack
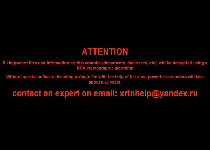
Messages delivered by the XRTN Ransomware over the course of its attacks will request that you contact a Russian e-mail address for assistance. However, malware analysts have found relying on suspicious admins of Trojans for technical support to be a dubious solution to file encryption attacks. Although the XRTN Ransomware does delete local backup data that would allow you to restore your files easily, its attacks are unable to target removable storage devices and cloud services that could serve as additional file backups. Finally, the XRTN Ransomware, like VaultCrypt, should be straightforward to remove by PC users who have anti-malware products installed on their machines.
The XRTN Ransomware has shown no signs of including the spyware components seen in VaultCrypt and makes no extensive use of typical Command & Control server communications. Nonetheless, the XRTN Ransomware infections may compromise your PC in ways not limited to harming your immediate file data. PC owners cleaning up the XRTN Ransomware infections should monitor bank accounts and other areas for potential breaches that could originate from passwords leaked through the XRTN Ransomware or a related threats.
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.