Super AV
Posted: December 28, 2011
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Threat Level: | 10/10 |
|---|---|
| Infected PCs: | 9 |
| First Seen: | December 28, 2011 |
|---|---|
| Last Seen: | April 18, 2018 |
| OS(es) Affected: | Windows |
 Super AV is a malicious anti-virus program that uses inaccurate pop-up alerts and scanner results to make it appear as though a horde of rootkits, keyloggers and other forms of high-level PC threats are infecting your computer. Even though Super AV has the appearance of a standard anti-virus scanner and offers to remove everything that Super AV detected if you'll spend money on registering Super AV, registration or purchase of Super AV is discouraged by SpywareRemove.com malware researchers who have found that Super AV has no genuine virus detection or removal features. As is commonly-true of rogue anti-virus programs, Super AV will continue to flood your screen with fraudulent alerts, regardless of the real state of your computer's health, until you remove Super AV with a real anti-malware program.
Super AV is a malicious anti-virus program that uses inaccurate pop-up alerts and scanner results to make it appear as though a horde of rootkits, keyloggers and other forms of high-level PC threats are infecting your computer. Even though Super AV has the appearance of a standard anti-virus scanner and offers to remove everything that Super AV detected if you'll spend money on registering Super AV, registration or purchase of Super AV is discouraged by SpywareRemove.com malware researchers who have found that Super AV has no genuine virus detection or removal features. As is commonly-true of rogue anti-virus programs, Super AV will continue to flood your screen with fraudulent alerts, regardless of the real state of your computer's health, until you remove Super AV with a real anti-malware program.
The Unimpressive Truth Underneath Super AV's Windows-Friendly Marketing
Super AV is a clone of other FakeScanti-based scamware such as Security Guard, Sysinternals Antivirus, WireShark Antivirus, Milestone Antivirus, BlueFlare Antivirus, Wolfram Antivirus, OpenCloud Antivirus, OpenCloud Security, Data Restore, AV Guard Online, Cloud Protection, AV Protection Online, System Protection 2012, AV Security 2012, Sphere Security 2012, AV Protection 2011, Security Guard 2012, Super AV 2013 and OpenCloud AV. As such, Super AV uses both the same interface and the same types of fraudulent pop-ups. Although Super AV tries to look professional with a generic shield icon and a Windows-standard type of firewall icon, all of Super AV's advertised features – its self-update function, its virus detection function, its system scanner and even its virus removal abilities are wholly-fake. You should ignore error messages and other warnings that may have originated from Super AV, since these warnings lack any basis in reality and may lead you into performing actions that are harmful for your PC.
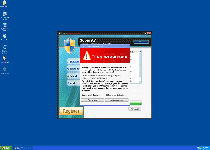
Examples of some of the warnings that Super AV may use include:
[Rogue program's name] – Malware Detected
Threats have been detected!
Warning! Some serious threats have been detected to your computer, that need to be removed instantly or they may cause critical damage to your computer!
[rogue program's name] can remove these viruses easily, and prevent damage to your personal computer.
If you click 'Remove viruses', you can protect your computer from destruction, however, if you click 'Continue unprotected', your identity can be compromised and you may lose all your important files and experience system slowdown.
Your system is infected!
Your computer is compromised by hackers, adware, malware and worms!
[Rogue program's name] can remove this infection. Please click this icon to remove threats.
Your computer is in danger!
[Rogue program's name] has detected some serious threats to your computer!
These viruses need to be eliminated immediately! Please click this icon to remote threats.
You should be equally-skeptical of Super AV's scanner results, which SpywareRemove.com malware analysts came about to be configured to display high-level PC threats like Backdoor.Sajdela, Worm.Reclog.A and Trojan.Hooblong.A without any effort to detect whether or not they're on your hard drive in the first place. Running actual anti-malware scanners will quickly show that Super AV's ability to detect real viruses or other PC threats is totally-nonexistent.
Super AV – Flying to Your PC and Then, Hopefully, Straight to the Garbage Bin
Infections by Super AV are often the result of unintentional visits to scamware websites that promote Super AV and other types of rogue security products. Drive-by-download scripts that install Super AV automatically via your browser can be turned off by disabling Java and Flash, although other vulnerabilities may also be exploited (and are, therefore, a justification for always having up-to-date anti-malware software on your PC).
Because Super AV is a simplistic creation of Napalm Rogue Builder, Super AV lacks many of the advanced features that independent scamware programs often utilize, but regardless, SpywareRemove.com malware research team warns that Super AV's presence should never be tolerated on your PC. Super AV can be removed by any competent anti-malware program as long as you've taken standard security measures to disable Super AV before scanning for Super AV.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%WINDIR%\bfctpwcb.exe
File name: bfctpwcb.exeSize: 1.03 MB (1034752 bytes)
MD5: 64a72b3a2a18ead767b4e0089cee2d6a
Detection count: 8
File type: Executable File
Mime Type: unknown/exe
Path: %WINDIR%
Group: Malware file
Last Updated: December 29, 2011
C:\WINDOWS\atexbees.exe
File name: C:\WINDOWS\atexbees.exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
%SystemDir%\[RANDOM].exe
File name: %SystemDir%\[RANDOM].exeMime Type: unknown/exe
Group: Malware file
Registry Modifications
HKEY..\..\..\..{Subkeys}[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]"Security" = "C:\Windows\atexbees.exe"HKEY..\..\..\..{RegistryKeys}HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exeHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe "Debugger" = "[RANDOM].exe"HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\..{RunKeys}HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run "Security" = "%Windows%\[RANDOM].exe"
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.